Modern networks rely on precise traffic control to keep data flowing smoothly while staying secure. One of the most important—yet often misunderstood—mechanisms behind this control is firewall port mapping. Whether you are hosting a game server at home, running a web application for customers, or managing enterprise infrastructure, understanding how ports are mapped can help you optimize performance and reduce security risks.
TLDR: Firewall port mapping is the process of directing incoming network traffic from one port to a specific device or service inside a private network. It works by translating public-facing ports to internal IP addresses and ports using rules defined in a firewall or router. This allows external users to access selected services while keeping the rest of the network protected. Correct configuration improves connectivity, but improper setup can expose systems to security threats.
What Is a Port and Why Does It Matter?
To understand port mapping, you first need to understand what a port is. In networking, a port is a virtual communication endpoint. While an IP address identifies a specific device on a network, a port identifies a specific service or application running on that device.
Think of it like an office building:
- The IP address is the building’s street address.
- The port number is a specific office inside that building.
For example:
- Port 80 is commonly used for HTTP (web traffic).
- Port 443 is used for HTTPS (secure web traffic).
- Port 25 handles SMTP (email sending).
Without ports, your device would not know whether incoming traffic is intended for a web server, an email service, or a gaming application.
What Is Firewall Port Mapping?
Firewall port mapping is the process of linking an external port on a public IP address to an internal IP address and port within a private network. This is often referred to as port forwarding, and while the terms are sometimes used interchangeably, port mapping typically emphasizes the translation aspect performed by network address translation (NAT).
In many home and business networks, devices use private IP addresses (such as 192.168.x.x). These addresses are not directly accessible from the internet. A router or firewall with a public IP acts as the gatekeeper, deciding which incoming traffic should be allowed and where it should be sent.
Port mapping creates a rule like this:
- External IP: 203.0.113.5
- External Port: 8080
- Internal IP: 192.168.1.10
- Internal Port: 80
This means that when someone visits 203.0.113.5:8080, the firewall forwards the request to the internal web server at 192.168.1.10:80.
How Firewall Port Mapping Works
At the heart of port mapping is Network Address Translation (NAT). NAT allows multiple devices in a private network to share a single public IP address.
Here’s how the process typically unfolds:
- An external user sends a request to your public IP address using a specific port.
- The firewall inspects the destination port of the incoming packet.
- If a matching port mapping rule exists, the firewall rewrites the destination IP and/or port number.
- The traffic is forwarded to the designated internal device.
- The internal device responds, and the firewall translates the source information back before sending it to the external user.
This translation happens in milliseconds and is invisible to users on both ends.
Types of Port Mapping
There are several kinds of port mapping configurations, each serving different needs.
1. Static Port Mapping
This is a permanent rule defined by an administrator. It is most commonly used for hosting services that need consistent accessibility, such as:
- Web servers
- Mail servers
- Remote desktop services
2. Dynamic Port Mapping
Dynamic mapping assigns ports automatically from a predefined pool. It’s often used in large-scale systems where connections are temporary and frequently changing.
3. PAT (Port Address Translation)
Also known as NAT overload, PAT allows many devices to share a single public IP by assigning unique source ports to each outgoing session.
Practical Use Cases
Firewall port mapping is used in various real-world scenarios:
Hosting a Website from Home
If you run a web server on your home computer, you must map port 80 or 443 from your router to your internal machine. Without this rule, external visitors cannot reach your server.
Online Gaming
Many multiplayer games require specific ports to be open for peer-to-peer connections. Port mapping ensures smoother connectivity and reduced latency.
Remote Work and VPN Access
Organizations use port forwarding to allow secure remote connections to internal resources, often through VPN gateways.
IP Cameras and IoT Devices
Security cameras and smart home devices often require port mapping for remote access—although modern solutions increasingly rely on cloud relays for security reasons.
Security Implications
While port mapping enables functionality, it also introduces risk. Every open port is a potential entry point for attackers.
Common risks include:
- Unauthorized access to exposed services
- Brute force attacks on login pages
- Exploitation of unpatched software
- Port scanning and reconnaissance
To mitigate these risks, best practices include:
- Only mapping ports that are absolutely necessary
- Using strong authentication methods
- Implementing firewall access control lists (ACLs)
- Enabling intrusion detection and prevention systems
- Keeping all services updated
Common Misconfigurations
Improper port mapping can cause both security and connectivity problems. Some frequent mistakes include:
- Forwarding the wrong internal IP address
- Using conflicting or already occupied ports
- Leaving unused ports open
- Forgetting to configure firewall rules to allow forwarded traffic
Even a small configuration error can result in failed connections or unintended exposure of sensitive systems.
Port Mapping vs. Port Triggering
Another concept often confused with port mapping is port triggering.
The key differences are:
- Port Mapping: Permanently forwards a port to a specific device.
- Port Triggering: Temporarily opens a port when an outbound connection is detected.
Port triggering is more dynamic and can be slightly safer for certain applications because ports close automatically after use.
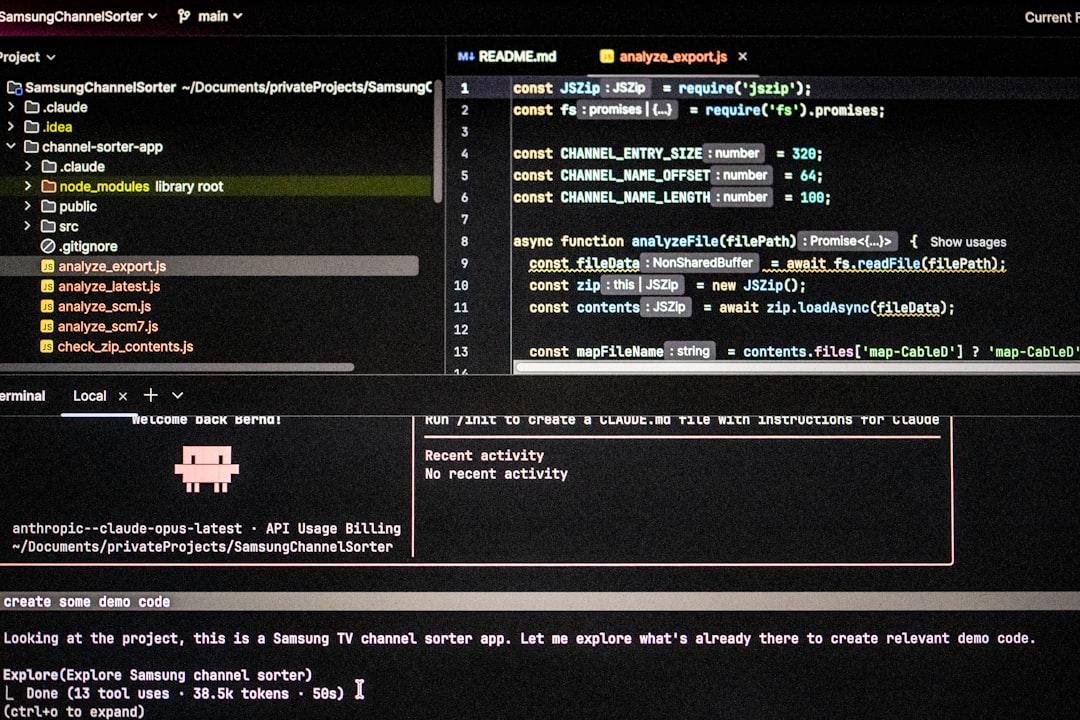
How to Configure Firewall Port Mapping
The exact steps depend on your hardware or firewall software, but the general process is similar:
- Log in to your router or firewall management interface.
- Locate the Port Forwarding or NAT section.
- Create a new rule specifying:
- External port number
- Internal IP address
- Internal port number
- Protocol (TCP, UDP, or both)
- Save and apply the configuration.
- Test the connection from an external network.
Advanced firewalls may also allow:
- Source IP restrictions
- Geolocation filtering
- Time-based access rules
Enterprise vs. Home Network Port Mapping
In home networks, port mapping is typically simple and handled directly through a consumer router interface.
In enterprise environments, however, port mapping often involves:
- Dedicated hardware firewalls
- Load balancers
- Reverse proxies
- Demilitarized zones (DMZs)
Large organizations may use layered security models where forwarded ports lead to intermediate systems rather than directly to internal servers.
Modern Alternatives and Trends
As cybersecurity threats evolve, organizations are moving away from traditional open port exposure whenever possible.
Emerging approaches include:
- Zero Trust architectures that verify every connection
- Cloud-based reverse proxies that hide internal infrastructure
- VPN-only access models for sensitive systems
- Software-defined perimeters
These methods reduce the need to expose services directly to the public internet, minimizing attack surfaces.
Final Thoughts
Firewall port mapping is a foundational networking concept that balances accessibility with security. By translating and directing traffic from public ports to internal systems, it enables everything from personal game servers to enterprise web applications.
However, every mapped port represents a deliberate choice: opening a door in your network’s perimeter. When configured correctly, port mapping empowers seamless connectivity and efficient service delivery. When mismanaged, it can become an open invitation to attackers.
Understanding how firewall port mapping works—its mechanics, risks, and best practices—helps you build networks that are not only functional but resilient. In an increasingly connected world, that knowledge is more valuable than ever.